Managed Detection & Response (MDR)
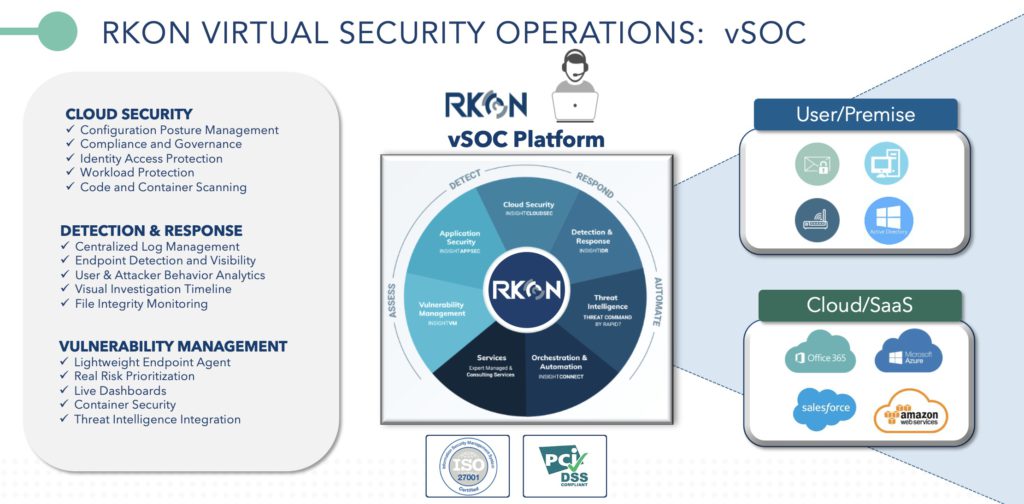
RKON’s Managed Threat Detection & Response is a core function of our ISO27001 certified Virtual Security Operations Center (vSOC). We offer end-to-end security, 24/7, operating at every stage of defense, from risk identification through to risk remediation and post-mortem incident review.
Our Managed Detection Response service unifies security data for log and event management in order to meet compliance, detect behavior behind breaches, contain threats before they become critical, and responds to problems quickly and confidently by accelerating investigations across users and assets. RKON’s comprehensive platform provides a single viewpoint for all IT instances from traditional data centers to cloud operations including Azure and AWS.
Security Log & Event Monitoring
As a managed detection response service provider, we leverage industry leading software to collect and aggregate logs from critical infrastructure components in the customer’s environment. RKON’s standard minimum log retention is 13 months with 18 months available for search, visualization, and investigations. These logs can be forwarded to our MDR platform or collected directly from the log source with numerous integrations, event sources, and raw data event sources. Our security experts prioritize event investigations and create customized reports to give deeper insights into your environment.
User Behavior Analytics
RKON’s security analysts leverage Rapid7 user behavior analytics to uncover patterns and insight to identify evidence of security breaches, insider threats, and risky behavior on your network. Network sensors continuously monitor network traffic at any location or site across your organization increasing visibility across the threat surface. Baseline normal activity to reliably detect attackers masking as company employees, lateral movement, and the use of stolen credentials. Get the jump on potential and occurring security threats with user behavior analytics.
Incident Management & Detection Response
To retain lightning-fast responses, we continuously scan for vulnerabilities, collecting data from across the infrastructure ecosystem in real-time, prioritizing risks and closing attack vectors before exposure. When behaviors are detected on your endpoints that indicate compromise, security alerts are immediately sent to notify RKON Security Analysts. Measures are then deployed to safely investigate, placing agents at endpoints for deep visibility, and collecting logs on the client’s virtual servers from infrastructure assets where an agent is unable to be installed.
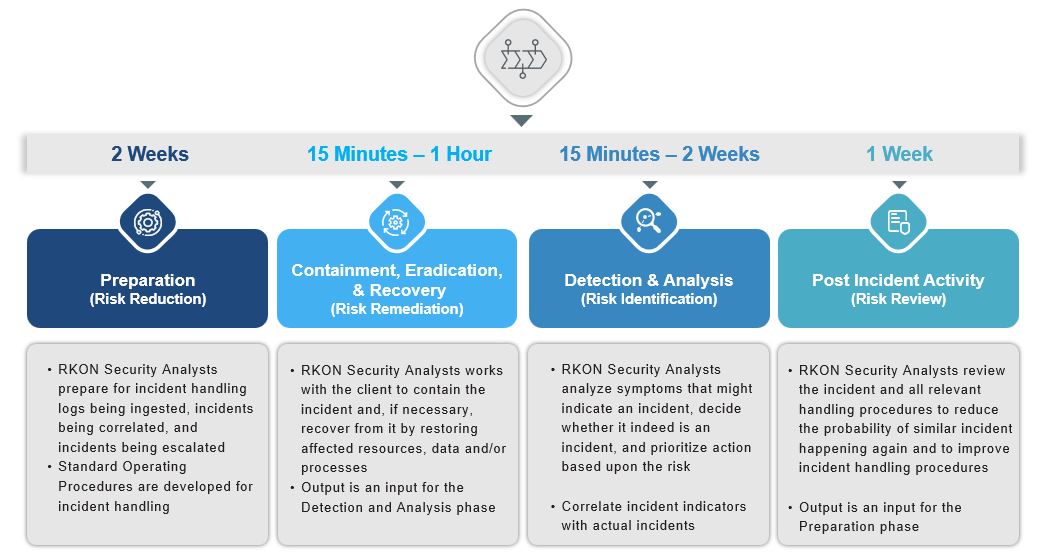
Our security analysts follow best practices for Security Incident Handling as set by industry standards to handle breaches quickly, efficiently, and effectively.
Why RKON For Managed Detection & Response
Security isn’t just about monitoring and reacting to incidents – it’s about understanding how to build, manage, and maintain a secure environment. RKON’s Managed Detection Response service aggregates and analyzes your data sources across logs, users, endpoints, and networks securing your organization before first signs of attack.
With over 20 years experience in security & incident response, we deliver world class IT on day one. Offering a complete security stack from threat management and vulnerability management, to our managed detection response service, we are not just helping others with their security, but we are an IT organization responsible for security. Contact RKON’s Security team today to learn more about our managed detection response services.
Contact Us Today
If you are looking for more information about our IT Transformation & Security services please don’t hesitate to reach out. Our team of IT experts is ready to help.