Your team automated the build, the test, and the deploy. Then the whole thing stalled waiting on a firewall ticket change request.
That bottleneck is not a process problem. It is an architecture problem, and it shows up in nearly every hybrid environment we work in. Teams migrating to the cloud carry on-premises network security assumptions that silently fail in cloud and hybrid architectures. Rework, delays, and gaps discovered at the worst possible time are the outcome.
Here is where those assumptions break.
The Mappings That Don’t Hold
Every one of these has a gap. The gap is where the breach lives.
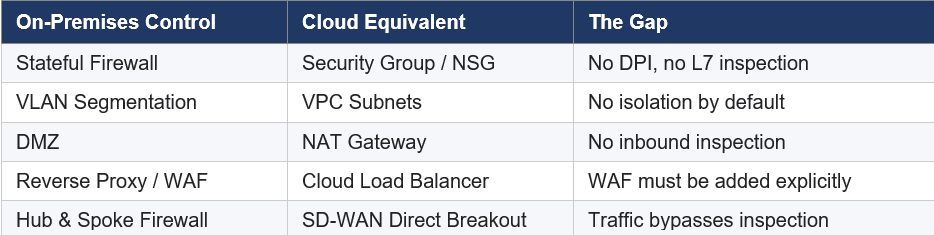
On-Premises Control
Cloud Equivalent
The Gap
Stateful Firewall
Security Group / NSG
No DPI, no L7 inspection
VLAN Segmentation
VPC Subnets
No isolation by default
DMZ
NAT Gateway
No inbound inspection
Reverse Proxy / WAF
Cloud Load Balancer
WAF must be added explicitly
Hub & Spoke Firewall
SD-WAN Direct Breakout
Traffic bypasses inspection
Security groups do port, protocol, and IP allow/deny at Layer 3/4. No application awareness, no threat signatures, no built-in logging. If you need L7 inspection, you need AWS Network Firewall or Azure Firewall Premium, explicitly routed through.
VPC subnets are a routing construct, not an enforcement boundary. Traffic between subnets in the same VPC routes directly by default with no firewall in the path. East-west lateral movement from a compromised workload can be completely invisible without additional controls.
NAT gateways handle outbound address translation. They do not inspect sessions, enforce inbound policy, or provide anything equivalent to bidirectional DMZ controls.
Cloud load balancers balance load. A WAF must be explicitly attached to every public ALB and is not on by default. Without it, there is no OWASP rule coverage and no bot mitigation.
SD-WAN Makes It Worse
SD-WAN direct internet breakout eliminates your centralized inspection chokepoint. Branch traffic reaches cloud workloads without crossing the data center firewall stack, and that is by design. SSL inspection at branch appliances is rarely performed because the performance cost is too high.
What follows is a split-brain problem: your SD-WAN dashboard shows traffic as tunneled and secure, while your VPC flow logs show direct traffic from those same source IPs. The DC firewall sees nothing. CISA Emergency Directive 26-03 (February 2026) confirmed active exploitation of Cisco Catalyst SD-WAN infrastructure, calling it a high-value target with known compromise in the wild, so this is not a theoretical concern.
Stop relying on the traffic path as your security control. Enforce security at the destination using cloud firewall ticket rules and security groups at the workload level.
Four Things to Do This Week for Firewall Ticket
- Enable VPC Flow Logs everywhere. All VPCs, all traffic, version 3+, retained 90 days minimum. Everything else on this list depends on it.
- Audit public ALBs for WAF coverage. AWS Console > WAF > check which ALBs have a Web ACL attached. Any that don’t are unprotected. Attach AWS Managed Rules Core Rule Set — it takes about 20 minutes.
- Run the split-brain test. Pull SD-WAN path analytics for your most sensitive traffic and cross-reference with VPC flow logs for the same source IPs. Gaps between the two mean broken routing.
- Audit security group rules. Flag every 0.0.0.0/0 inbound rule. AWS Config rule ‘restricted-common-ports’ does this automatically.
Fix the network architecture and your teams ship faster, without firewall tickets blocking deployments or rearchitecting mid-migration.
Join Tyler at GrassRootz for the full talk on June 4th for more: https://grassr00tz.com/

Author: Tyler Coady, Senior Cloud Security Consultant, RKON

